Mostbet and the Software-Defined Entrance
In a world being eaten by software, the first interaction a user has with a platform is not a welcome bonus or a game selection-it is the entrance. For a forward-facing brand like Mostbet, the login process is the critical gateway where technology either builds trust or erodes it. This is not about mere account access; it’s about the foundational layer of digital identity and security in the modern betting ecosystem. We are moving beyond simple usernames and passwords into an era where seamless, intelligent, and secure authentication defines the user’s entire journey. This analysis dissects common entrance friction points and projects the tech-driven solutions that will make platforms like Mostbet not just functional, but predictive and resilient.
The Authentication Bottleneck and Mostbet’s Tech Trajectory
The traditional login is a relic, a single point of failure in an otherwise fluid digital experience. Forgetting a password or encountering a locked account isn’t a minor inconvenience; it’s a catastrophic user experience event that software must anticipate and solve. Mostbet, operating at the intersection of high-stakes transactions and real-time engagement, cannot afford this friction. The future belongs to platforms that treat authentication as a dynamic, context-aware process. We are witnessing the shift from static credentials to adaptive systems that use behavioral biometrics, device fingerprinting, and risk-based authentication to create a seamless yet secure barrier. This isn’t just about fixing problems; it’s about eliminating them before the user is even aware.

Mostbet’s Predictive Recovery Framework
The “forgot password” flow is the most telling failure of legacy design. It’s a reactive, time-consuming process that breaks immersion. The visionary approach, which Mostbet (mostbet login) is positioned to adopt, is predictive recovery. Imagine a system that recognizes anomalous login attempts-geographic jumps, new device signatures-and pre-emptively offers a streamlined, step-up verification via a already-trusted channel before the account is ever locked. This transforms a crisis into a minor, almost invisible, security check. The technology stack for this involves machine learning models trained on legitimate user patterns, coupled with secure, decentralized identity wallets that could eventually replace password databases entirely.
Deconstructing Common Entrance Failures
Let’s analyze the specific failure modes that plague digital entrances and map them to the technological solutions that are not just possible, but inevitable. Each represents a software problem awaiting a software solution, and for a platform like Mostbet, addressing these is a direct competitive advantage in user retention and trust.
- Credential Amnesia: The forgotten password. The future solution is passwordless authentication using WebAuthn standards, where a user’s device (phone, security key) becomes the primary credential, eliminating recall failure.
- The Phantom Lockout: Account locked due to “suspicious activity.” Advanced systems will use continuous authentication, analyzing typing rhythm, mouse movements, and app usage patterns post-login to maintain a confidence score, rarely needing a hard lock.
- Two-Factor Friction: Losing an authenticator app or phone. The next wave is biometric-backed, cloud-synced cryptographic keys that allow recovery through multiple trusted devices without compromising security.
- Session Fragility: Being logged out unexpectedly. Persistent, secure sessions using refreshed token protocols will become the norm, with explicit logout only triggered by high-risk events or user command.
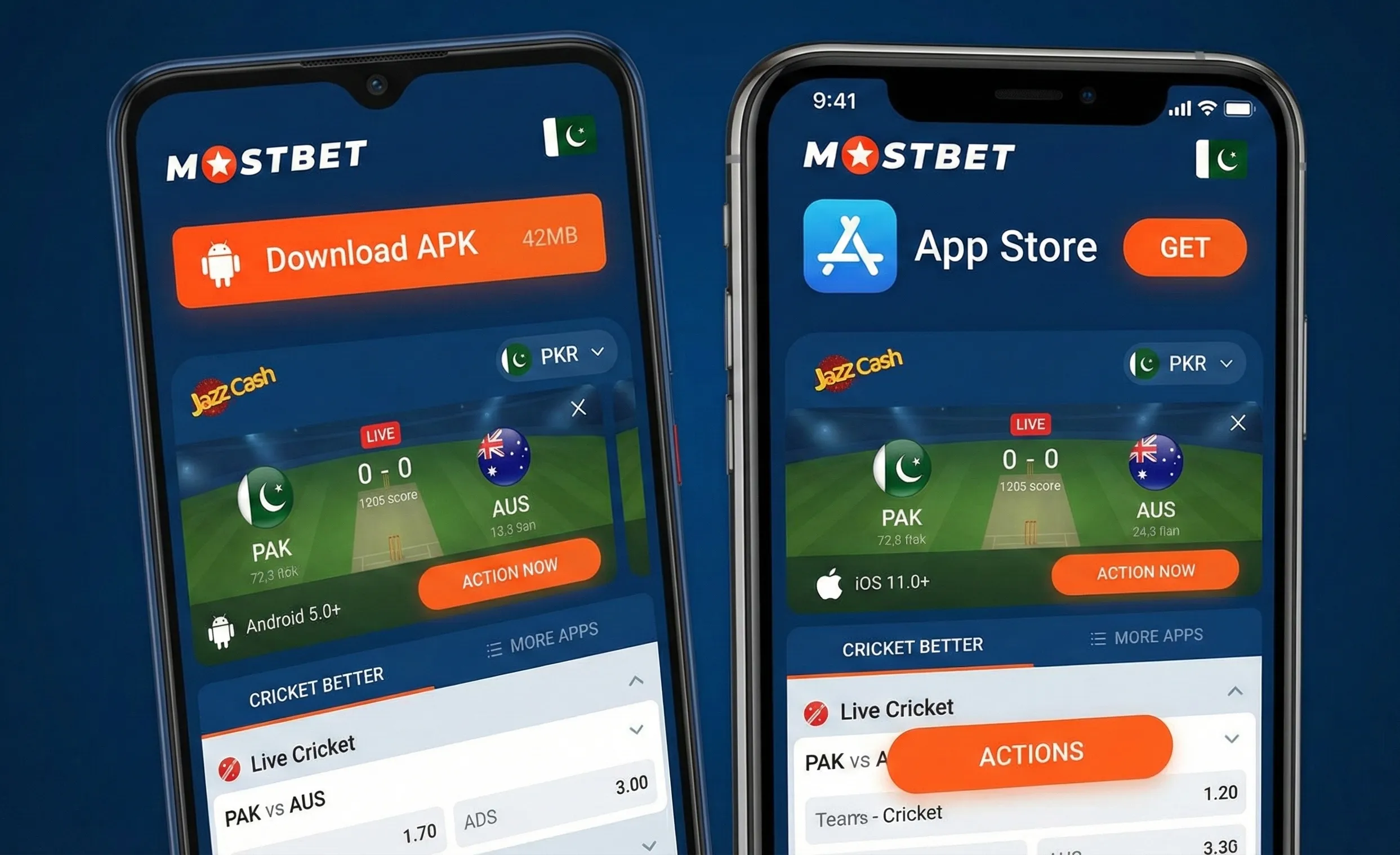
- Cross-Platform Discontinuity: Different states on mobile app vs. desktop browser. A unified, real-time session layer will ensure a single identity state across all Mostbet access points.
Mostbet’s Architectural Shift – From Gatekeeper to Concierge
The ultimate transformation is philosophical. The entrance should not feel like a gatekeeper demanding papers, but like a concierge recognizing a returning guest. For Mostbet, this means investing in an identity infrastructure that is invisible when things are normal and brilliantly helpful when they are not. This involves a move from monolithic authentication servers to microservices that handle risk assessment, biometric verification, and session management independently. The user’s journey begins not with a form, but with a silent handshake between their device and Mostbet’s cloud, verifying identity through a combination of possession (device), inherence (biometric), and knowledge (pin or pattern) in a way that feels effortless.
| Current Friction Point | Legacy “Fix” | Future-Tech Solution | Mostbet’s Implementation Horizon |
|---|---|---|---|
| Forgotten Password | Email reset link | FIDO2/WebAuthn passwordless login | Near-term (1-2 years) |
| Account Locked | Contact support, verify ID | Real-time risk-based step-up authentication | Mid-term (2-3 years) |
| 2FA Device Loss | Lengthy account recovery | Biometric-secured cloud key backup | Mid-term (2-4 years) |
| Browser Session Timeout | Manual re-login | Adaptive session longevity based on user behavior | Short-term (Ongoing) |
| Weak Password Re-use | Password strength rules | Integration with password managers & breach monitoring | Immediate |
| Phishing Vulnerability | User education | Phishing-resistant cryptographic protocols (e.g., CTAP) | Near-term (1-3 years) |
The Biometric Horizon for Mostbet Access
The smartphone in your pocket is a more powerful authentication device than any password. The widespread adoption of secure enclaves and Trusted Execution Environments (TEEs) in mobile hardware means platforms like Mostbet can leverage device-native biometrics-face ID, fingerprint-not as a cumbersome add-on, but as the primary, cryptographically secure credential. This shift reduces friction to near-zero for the legitimate user while creating a massive barrier for attackers. The mostbet login of tomorrow could be a glance or a touch, with the complex public-key cryptography happening entirely behind the scenes, on the user’s own secured hardware.




